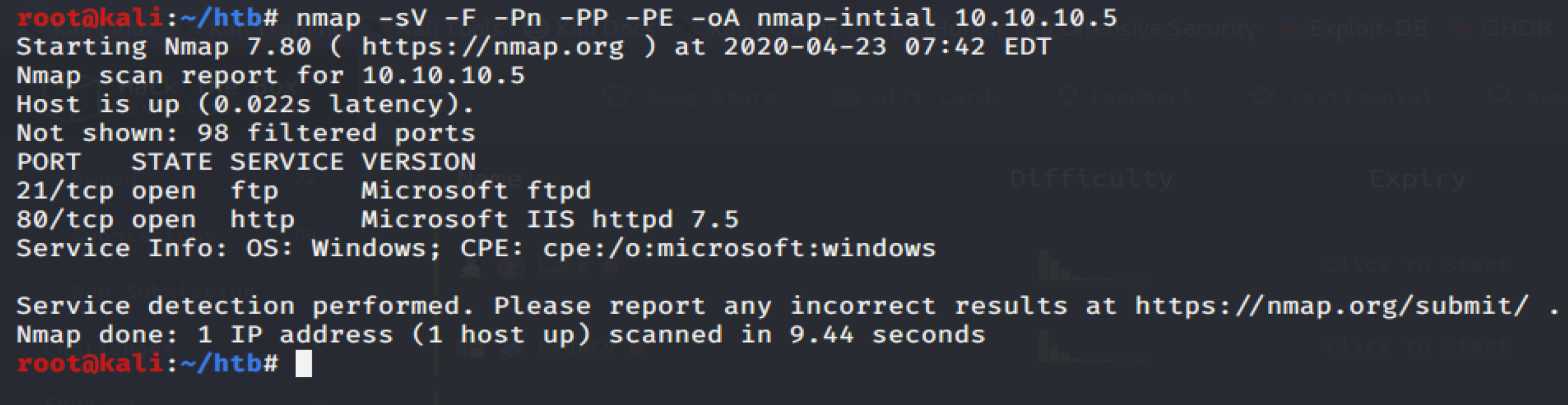
In Microsoft Endpoint Configuration Manager, click Assets and Compliance Endpoint Protection Windows Defender Exploit Guard. Click Home Create Exploit Guard Policy. Enter a name and a description, click Exploit protection, and click Next. Browse to the location of the exploit protection XML file and click Next. Less than a week after the publication of exploit code for a critical vulnerability in the FTP Service in Microsoft Internet Information Services (IIS), attackers are now launching in-the-wild. Microsoft IIS FTP Server LIST Stack Exhaustion This module triggers Denial of Service condition in the Microsoft Internet Information Services (IIS) FTP Server 5.0 through 7.0 via a list (ls) -R command containing a wildcard. 220 Microsoft Ftp Service X0d X0a Exploit Microsoft IIS FTPd NLST Remote Buffer Overflow Vulnerability Microsoft IIS is prone to a remote stack-based buffer-overflow vulnerability affecting the application's FTP server. An attacker can exploit this issue to execute arbitrary code within the.
Severity: High
8 February, 2011
Summary:
- This vulnerability affects: The IIS FTP service running on Windows Vista, 2008, 7, and 2008 R2
- How an attacker exploits it: By sending a specially crafted FTP command
- Impact: In the worst case, an attacker gains complete control of your IIS server
- What to do: Deploy the appropriate IIS update immediately, or let Windows Automatic Update do it for you
Exposure:
Internet Information Services (IIS) is the popular web and ftp server that ships with all server versions of Windows.
In a security bulletin released today as part of Patch Day, Microsoft describes a serious vulnerability that affects the optional FTP server that comes with the latest versions of IIS. Specifically, the IIS FTP service suffers from a buffer overflow vulnerability involving the way it handles a specially crafted FTP commands (or more specifically, specially encoded characters in an FTP response). By sending such a malformed FTP command, an attacker could exploit this vulnerability to either put your FTP server into a Denial of Service (DoS) state, or to gain complete control of it. An attacker does not have to authenticate to your FTP server to launch this attack.
However, IIS does not install or start the IIS FTP service by default. You are only vulnerable to this attack if you have specifically installed and started this service. That said, many administrators do enable IIS’s FTP service in order to give web administrators an easy way to update their web sites. If you are one of those administrators, you should consider this flaw a serious risk.
Researchers have already publicly released Proof-of-Concept (PoC) exploit code demonstrating the DoS version of this flaw. Whether or not you are using the IIS FTP service, we still recommend you download, test and install this update as soon as you can. Being a critical server update, we highly recommend you test it on non-production servers before pushing it to your real web site.
Solution Path:
Download, test, and deploy the appropriate IIS patches immediately, or let Windows Automatic Update do it for you.
- For Windows Vista (w/SP1 or SP2)
- For Windows Vista x64 (w/SP1 or SP2)
- For Windows Server 2008 (w/SP2)
- For Windows Server 2008 x64 (w/SP2)
- For Windows 7
- For Windows 7 x64
- For Windows Server R2 2008 x64
- For Windows Server R2 2008 Itanium
For All WatchGuard Users:
This attack leverages seemingly normal FTP response traffic. You should apply the updates above.
Status:
Microsoft has released patches to fix this vulnerability
References:
Microsoft Ftp Service Exploit Software
This alert was researched and written by Corey Nachreiner, CISSP.
Microsoft Ftp Service 5.0 Exploit
What did you think of this alert? Let us know at [email protected].

More alerts and articles: Log into the LiveSecurity Archive.
Related Posts
